Sometime on the morning of Sunday, 19 July 2020, the GEDmatch site was either hacked or experienced a severe programming failure. DNA kit privacy has been breached? Kits that were marked “private” or “research”, meaning they should not show in the match lists of anyone else, because visible, and kits that had opted out of law enforcement matching were opted in.
This is a breaking story. I will update as more information becomes available. If you have screen shots you’re willing to share, please let me know.
Update 9:00 AM Pacific Time, 19 July (Sunday)
I was briefly able to get into GEDmatch. My one remaining kit is a post-mortem DNA analysis with low data quality. It should neither be part of the main matching pool nor opted in to law enforcement matching. At last check, it was both.

The site went down again before I was able to change the kit settings.
On social media, people are reporting seeing kits with Parabon email addresses. This, it appears that even the law enforcement kits were exposed to public matching. I wonder how many there are.
Update 9:40 AM Pacific Time, 19 July (Sunday)
A reader, who wishes to remain anonymous, sent this screenshot. It includes a Doe kit (unidentified deceased person) as well as what are likely experimental kits (“randompartial”) not meant for general matching.

Update 10:00 AM Pacific Time, 19 July (Sunday)
I was able to log in. The settings on my kit have been reset to their original state, and I was not able to find any law enforcement or Doe kits in the match lists of five randomly selected kits. The problem appears to be fixed for now.
Update 11 AM Pacific Time, 19 July (Sunday)
I’ve learned that kits from the European Union that are protected by GDPR privacy laws were also affected. I’m no expert on GDPR, but as I understand it, GEDmatch will have to report the breach to authorities within 72 hours and may be subject to fines.
I’m also hearing reports that some people have lost kits from their accounts.
Now is a good time to remind readers that GEDmatch does not and has never gotten fully informed consent for law enforcement matching. More information is here.
Update 3:30 PM Pacific Time, 19 July (Sunday)
TechCrunch reports that Brett Williams, the CEO of GEDmatch’s parent company “would not say, when asked, if Verogen or Gedmatch have received any law enforcement requests for user data in the past day, or if either company has responded.”
Update 5 PM Pacific Time, 20 July (Monday)
Although GEDmatch posted a statement yesterday evening on their Facebook page saying the problems were fixed, they weren’t.

Today, around 4:30 PM PDT, research kits (which should not be visible in general searches) were once again added to the public matching database. The site was taken down again about 15 minutes later.
GEDmatch has still explained what went wrong, nor have they apologized to their users for the privacy breaches.
Update 5:45 PM Pacific Time, 20 July (Monday)
GEDmatch issued a second statement acknowledging that they were hacked by one of their users. It’s unclear whether today’s problems were a second hack.
Update 9:15 AM Pacific Time, 21 July (Tuesday)
GEDmatch announced on their Facebook page that they would be offline for up to 3 days. I have not yet received an email notification from them, so they appear to have not notified their users directly.

Update ≈3 PM Pacific Time, 21 July (Tuesday)
MyHeritage alerted its customers that they were the target of a phishing attack that they believe was tied to the GEDmatch hack. Read more here.
Update 3:30 PM Pacific Time, 21 July (Tuesday)
In two separate statements on their official Facebook page, GEDmatch states that they encrypt the DNA data.

However, their Site Policy (archived 27 May 2020) explicitly says that the data is not encrypted.

Update 7:30 AM Pacific Time, 22 July (Wednesday)
GEDmatch emailed their users to alert them to the security breach. The email in full read:
Dear GEDmatch member,
On the morning of July 19, GEDmatch experienced a security breach orchestrated through a sophisticated attack on one of our servers via an existing user account. We became aware of the situation a short time later and immediately took the site down. As a result of this breach, all user permissions were reset, making all profiles visible to all users. This was the case for approximately 3 hours. During this time, users who did not opt-in for law enforcement matching were available for law enforcement matching, and, conversely, all law enforcement profiles were made visible to GEDmatch users.
On Monday, July 20, as we continued to investigate the incident and work on a permanent solution to safeguard against threats of this nature, we discovered that the site was still vulnerable and made the decision to take the site down until such time that we can be absolutely sure that user data is protected against potential attacks. It was later confirmed that GEDmatch was the target of a second breach in which all user permissions were set to opt-out of law enforcement matching.
We can assure you that your DNA information was not compromised, as GEDmatch does not store raw DNA files on the site. When you upload your data, the information is encoded, and the raw file deleted. This is one of the ways we protect our users’ most sensitive information.
Further, we are working with a leading cybersecurity firm to conduct a comprehensive forensic review and help us implement the best possible security measures. We expect the site will be up within the next day or two.
We have reported the unauthorized access to the appropriate authorities and continue to work toward identifying the individuals responsible for this criminal act.
Today, we were informed that MyHeritage customers who are also GEDmatch users were the target of a phishing scam. Please remember to exercise caution when opening emails and clicking links. Never provide sensitive information via email. If an email seems suspicious, contact the company in question directly through the phone number or email address listed on their website, not via a reply to the suspicious email. You can reach GEDmatch at gedmatch@verogen.com or (858) 285-4101. At this time, we have no evidence to suggest the phishing scam is a result of the GEDmatch security breach this week. We are continuing to investigate the incident.
Please be assured that we take these matters very seriously. Our Number 1 responsibility is to protect the data of our users. We know we have not lived up to this responsibility this week, and we are working hard to regain your trust. We apologize for the concern and frustration this situation has caused.
Sincerely,
Brett Williams
CEO, Verogen Inc.
Additional Reading
Peter Aldhous, A Security Breach Exposed More Than One Million DNA Profiles On A Major Genealogy Database, BuzzFeed News, 22 July 2020.
Debbie Cruwys Kennett, Major privacy breach at GEDmatch, Cruwys News Blog, 19 July 2020.
Zach Whittaker, Gedmatch investigating after user DNA data made available to police, TechCrunch, 19 July 2020.

Thank you for alerting us! Your are great!
Yes, I checked mine and just changed them back. My original kits were open to the police anyway, and the others were just duplicates. For me, no biggie.
You were hacked. That is a biggie. Right now you have no idea what information they have. You know they have your email address. I would at least change your password.
Can they get your raw dna data and use it for illegal or other purposes though ?
I can’t answer that. The way GEDmatch processes uploads, it would take some work to recreate the raw data, but it might be possible.
The site is down on my end. As soon as this came my email through I went to Gedmatch. My intent was to delete private kits and kits I manage that haven’t given permission to be opted into law enforcement matching. Once Gedmatch comes back online I will probably remove all my DNA kits. This is very concerning.
I was able to get in very briefly, just long enough to see that my one remaining kit had been opted in, but not long enough to fix the settings. I’m glad I deleted all of my other kits way back when.
I haven’t been in Gedmatch since it was sold. When I logged in I had to agree to their privacy policy which I did not, so I opted to decline and delete all my kits. I just hope the kits actually get deleted. I don’t expect a ton of privacy on the internet, but I do expect that settings I have selected and terms I agree to will be adhered to. I was on the fence when it was sold, but I also mistakenly thought there would be strong security protocols and protections from a corporation over a one man show who seemed to change terms of service on a whim. I’m in support of LE, but that was only my choice to make on my kit only. This mornings breach or failure lost my faith in this new owner. I don’t have time to really work on DNA lately, so for me it seems like a good time to just pull out.
Erin, I am in the same situation as you – I had not logged in since GEDmatch was sold, as I was trying to decide what to do. I only had two kits left there, as I have been participating in an ethnic GEDmatch group on Facebook and was trying to decide if I wanted to run their matches in that group any more. So yours and my kits technically should not have been active since we hadn’t agreed to the terms – I know my two kits haven’t shown up as matches to anyone else in the Facebook group since the sale. I think I’m going to go ahead and accept the terms, run my matches once more, then delete my kits – so that I can – hopefully – be SURE they actually get deleted. Then delete my account. Like you, I’ve totally lost faith in the new owner.
I never expected privacy because it is online and it is open season for anything online. Guess more people will pull out of Genetic DNA.
I do expect the companies entrusted with the genetic data of millions of people to protect that data.
The site appears to be down right now.
I was able to get in briefly, but then it went down again.
The gedmatch site is down for maintance – Currently No ETA
thats the notice i received
I was able to get in briefly, but then it went down again.
Yikes! Hope it’s a server issue & nothing of consequence.
Site url is still down as of 1 pm Eastern time.
A server issue shouldn’t cause research kits to become public. Looks like the site is back up and fixed as of 10 am Pacific.
I just looked at my kits and matches and I don’t see what you are seeing. Mine look just like they looked before.
GEDmatch appears to have fixed the problem.
I am now able to log in to GEDmatch (after issues earlier). Is it “safe” to use?
I cannot speak to how safe GEDmatch is to use.
I don’t know if they did a recovery but mine all looks good. All of my kits are as I had set them.
My one remaining kit has returned to normal, as well. I’m hearing reports of kits that have gone missing.
A friend notified me of your post. I went right away to check on my account at GEDmatch. This was about 12:40pm. At first I got an error message about maintenance, but I kept trying and it let me in finally.
All of the kits that I have marked “Research” and “opted out” are all as they should be. My email address looks fine, too.
I hope and pray no one was able to see those research kits as that was a condition of me having access to their DNA for my research.
Thanks for letting us know!
I removed the bit about emails being altered because I can’t independently confirm it. Yes, the research kits were visible, and I’ve even seen people commenting that they know they’re not supposed to see those kits but they’re saving the data anyway.
Thank you. I understand that research kits were visible. I just hope not ALL of them were. I was just saying that I hope these particular ones were not. I have to keep hoping these particular ones weren’t visible, or that no one that would cause problems saw them.
As far as I’ve been able to tell, ALL research kits were affected.
19 July 2020 13:55 EDT — just went to the site and did not see any of what you described. All looked normal.
They appear to have fixed most of the problems.
Thank you. Then, all I can do is pray for no fall-out. 🙁
Fingers crossed.
Thank you. GEDmatch is back to having the error message again, with “no ETA for availability”.
If they don’t get it fixed and back up (and staying up!) soon, I wonder what they will do in regards to their Tier 1 members. It is very frustrating to pay for something, then not be able to use it.
I’m back in GEDmatch and it seems to be working okay.
GEDmatch site states they are down for maintenance.
As of right now, and for the past couple of hours, there is nothing at the IP address for gedmatch.com . That address is in the AWS address space, so presumably it is a load-balancer address … essentially, one “front door” that provides access to the rest of the service.
I am not privy to how GEDMatch is designed architecturally, or what their staffing resources are. In the case of a systems error that could not be “rolled back” to a previous version of the code, spinning up a server with a single-page web site that states something like “GEDMatch has been taken offline temporarily due to technical difficulties. Please retry later.” would be relatively trivial.
The fact that they did the technical equivalent of “pulling the plug” seems to indicate a data breach or a systems compromise rather than some sort instead of a programming error or systems failure. Also, most “sane” computer operations do not make changes to live production systems on a weekend.
Thanks for that insight.
Sadly, anything can be hacked! Do what you can but, it is an impossible task to keep something hidden from someone with talent that wants to see it! It is the nature of IT!
Some sites have better track records than others.
I used PayPal to pay for the Tier 1 so I hope they weren’t able break thru to PayPal.
We still don’t know whether they were hacked or whether this was a programming error on their part.
Blank page now with “ The gedmatch site is down for maintance – Currently No ETA”
By 6pm on 6/19/2020 seems to be working ok. I had no apparent problems with moving or getting data on any tool. All my research kits are still listed as research.
Regards, Arthur
It appears that ALL kits were exposed for a time, even research kits.
I just logged onto my account and all is normal, email, privacy and I still see all the same people at the top half of my list of matches. I would include a screenshot however in private only.
It’s been fixed.
nothing seems to have changed on my account (I manage many kits) or it has been fixed
It’s been fixed. The entire database appears to have been affected.
Thanks for the alert, Leah. As of 9:30 PM EDT Sunday, everything looks normal on my account. Police settings are as I made them. Research settings are as I made them. So whatever the problem was this morning, it is gone now.
Yes, it’s been fixed. No official word yet on what caused the problem (hack or programming error).
It’s down again: “The gedmatch site is down for maintenance – Currently No ETA”
Just before it went down an hour or two ago it would not let me delete kits, and my top results again included very odd looking “matches” and email addresses. So it seems “it” — whatever this issue really is — was not resolved yesterday, like they said.
They’ve now determined that they were hacked yesterday (Sunday). I don’t know whether they were hacked again today, but research and private kits were put back into the public database briefly this afternoon. GEDmatch took the site down again until they can resolve the problem.
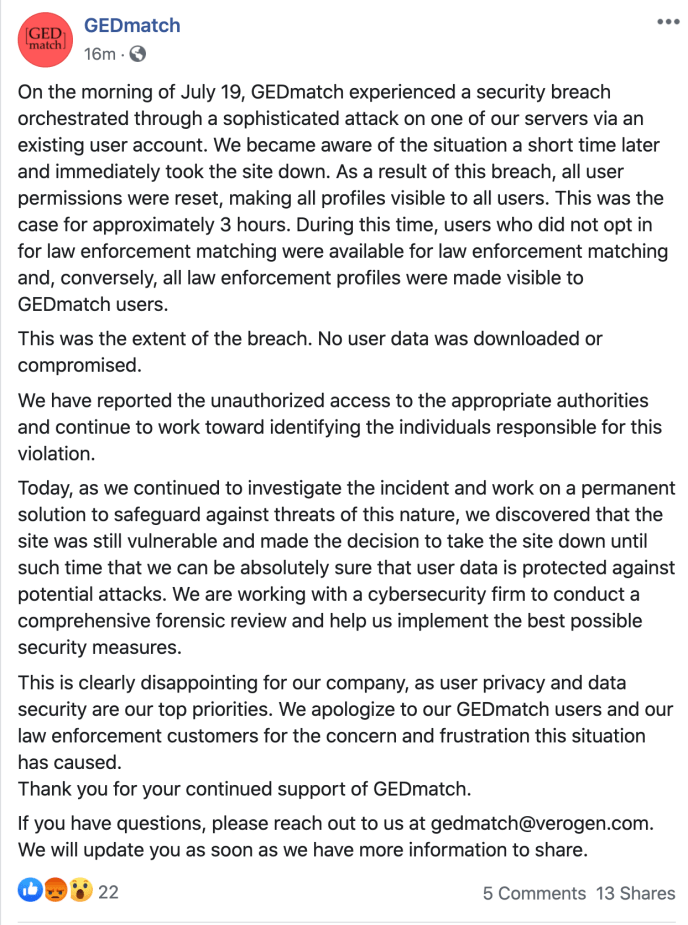
Gedmatch page on Facebook post this about 3 hours ago.
I’m thinking just because I had not been to the site since the sale and agreed to their terms of service since the change over it didn’t matter and my kits were exposed anyway. Someone had previously suggested my kits weren’t visible since I had not agreed to the new terms of service. It sounds to me like anyone and everyone was exposed. Even though I deleted yesterday when the site came back online I have no confidence that this took and my information removed from their systems as other have experienced issues deleting. I will be keeping an eye on this.
From gedmatch @ facebook tonight:
On the morning of July 19, GEDmatch experienced a security breach orchestrated through a sophisticated attack on one of our servers via an existing user account. We became aware of the situation a short time later and immediately took the site down. As a result of this breach, all user permissions were reset, making all profiles visible to all users. This was the case for approximately 3 hours. During this time, users who did not opt in for law enforcement matching were available for law enforcement matching and, conversely, all law enforcement profiles were made visible to GEDmatch users.
This was the extent of the breach. No user data was downloaded or compromised.
We have reported the unauthorized access to the appropriate authorities and continue to work toward identifying the individuals responsible for this violation.
Today, as we continued to investigate the incident and work on a permanent solution to safeguard against threats of this nature, we discovered that the site was still vulnerable and made the decision to take the site down until such time that we can be absolutely sure that user data is protected against potential attacks. We are working with a cybersecurity firm to conduct a comprehensive forensic review and help us implement the best possible security measures.
This is clearly disappointing for our company, as user privacy and data security are our top priorities. We apologize to our GEDmatch users and our law enforcement customers for the concern and frustration this situation has caused.
Thank you for your continued support of GEDmatch.
If you have questions, please reach out to us at gedmatch@verogen.com. We will update you as soon as we have more information to share.
It’s the 21st July and the site says ‘The gedmatch site is down for maintenance – Currently No ETA’. with no ability to log in. Not good.
https://www.eurekalert.org/pub_releases/2020-01/uoc–hds010620.php
Thanks for sharing this link to the news release from UC Davis (“Hobbyist DNA services may be open to genetic hacking”) describing vulnerabilities in GEDmatch. You can read more about that study here: https://thednageek.com/the-whole-of-the-moon/
Hi, thanks for your comprehensive article which was written over a year ago to date. Have you heard any recent updates? I attempted to log in for the first time today, and was presented with the options to accept or reject the terms. But when I selected Option #2 – Reject to delete my GEDmatch registration and remove all data from their servers, it goes to a “page not found” error page. Do you know what that’s about?
GEDmatch had a couple of back-to-back breaches in July had nothing (at least not public) since then. You must accept the new Terms of Service to use the site. If you’re not sure what you want to do, you can accept the ToS, look through the site, then delete all of your kits if you’re not comfortable with their new focus on law enforcement.